Job Recruitment Impersonation Scams

Job recruitment scams occur when threat actors reach out to victims through different online messaging platforms from seemingly reputable organisations offering victims a well-paid job opportunity with minimal work. However, these job offers do not lead victims to prosperity and job satisfaction. Instead, victims are exploited and left behind with a non existent job, identity theft and, in some cases, monetary loss as well. Additionally, the company’s that are impersonated in these attacks face reputational consequences, ultimately putting their brand image at risk.
These scams became more popular with the Covid-19 pandemic where business communications started taking place online, leading to an increase in remote positions and employees becoming dependent on online methods of communication. With individuals seeking more remote working opportunities, threat actors found an opening to meet this demand by targeting job seekers with appealing remote jobs. As reported by the U.S. Federal Trade Commission, while the amount of job recruitment related scams were averaging 25 thousand per quarter prior to the pandemic, today that number has quadrupled, totalling over 97 thousand in Q3 of 2022.
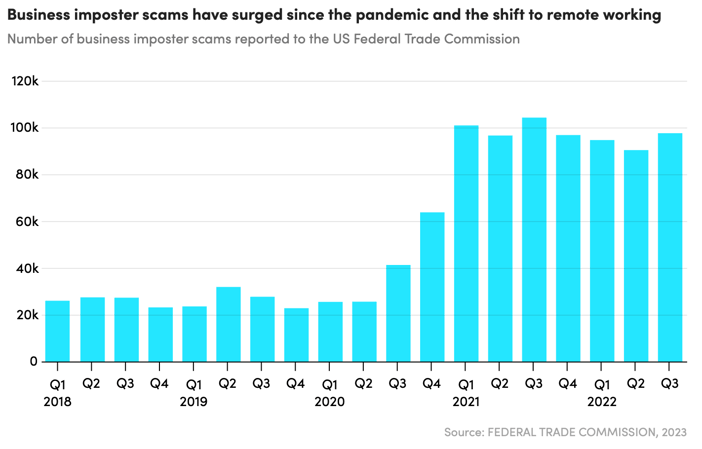

As January and February are considered some of the peak months for job searchers, threat actors are expected to increase their efforts scamming people into 'signing on' with their fake and brand impersonated job offers.
How do these brand impersonation scams work?
Threat actors use text messages, emails, social media, fake job ads and fake LinkedIn profiles to spread fake job offers, often employing multiple avenues of communication in order to gain a wide reach and higher likelihood of success. To inspire trust in the messages they send and/or post online, threat actors employ brand impersonation tactics. This occurs when a threat actor uses a brand's logo, colours, font, and so on, to ensure recognition and inspire trust with victims.
As brands today all have some form of online presence (websites, mobile applications, social media accounts), replicating and impersonating a brand is a relatively simple task for threat actors to accomplish. In these job offers, threat actors will often include a valid looking link to a fake website that through brand impersonation looks genuine and similar to the legitimate site. This helps inspire even more trust with the victim, leading them to believe that the job offer is the product of the legitimate company.
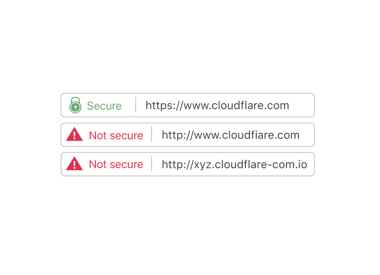
To do this, threat actors first register a domain that is similar to the target company before adding the link in an email, for example, as illustrated in the images below.
The website visited by victims will be a clone or close copy the content from the legitimate target website, which the threat actors will have altered to fit their 'story'. The images below represent an example of this. In this instance threat actors have taken the legitimate hiring page from Spirit Airlines (on the left) and created a brand impersonated hiring website (on the right) that is very similar, but with noticeable differences. The most interesting factor is that the brand impersonated site is asking victims to upload “… drivers license both front and back page“, which is not mentioned anywhere on the legitimate website and shows a clear attempt to steal the victims personal information.
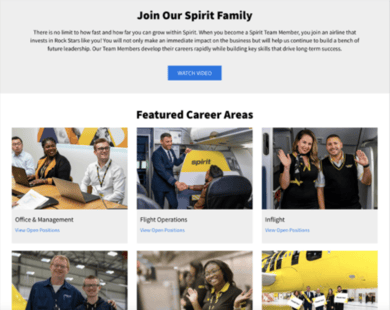
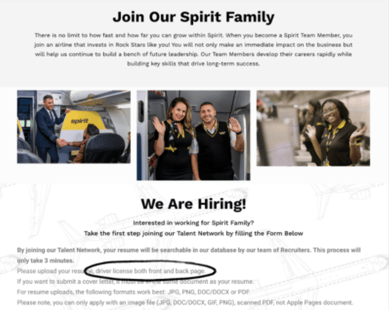 . Legitimate job site Brand Impersonated Job Site
. Legitimate job site Brand Impersonated Job Site
When a victim responds to these scams, they often move forward quickly with a short interview process involving little interaction between the threat actor and the victim. In some instances, victims have merely been asked to answer a short online brand impersonated questionnaire or send a one way recording of themselves wherein they answer questions regarding their skills and experience, before being asked to sign a contract. While this may sound ludicrous, some companies have a fast hiring process, making this method not highly illogical. Companies are generally employing a more relaxed and less formal approach to job seekers today allowing wide ranging methods of interaction. Threat actors exploit this by issuing scams that follow the same methods, leaving victims less likely to contradict and question the application process due to the new and faster norm of communication.
Threat actor goals
With these scams, threat actors are attempting to persuade jobseekers into sharing personal information that would allow them to conduct identity theft. In certain cases, attackers have also attempted to steal their money from jobseekers via different methods, including:
-
asking victims to send money in order to buy remote-work supplies and tools with promises of reimbursing the expenses.
-
requiring the victim's bank account details to ensure direct deposits for salary purposes, and
-
by offering the victim a sign-on bonus via a fake cheque (it can take weeks before a fake bank cheque is identified), then informing the victim that they need to transfer some of it back as too much money was sent by mistake.
Who is targeted?
Theses scams most often target and impact vulnerable individuals desperate for employment, including recent university graduates who are seeking their first jobs and unemployed individuals desperate to pay their bills. On the other hand, threat actors also target senior business individuals to get more value for their efforts. To avoid these job recruitment scams, keep and eye out for, and remain sceptical of:
-
Job offers that seem too good to be true
-
Obvious spelling mistakes in the job offer and later correspondence
-
Being hired with little effort and no face-to-face interaction
-
Being asked to send money or pay for services
-
Requests for sensitive personal information
Impact to your brand
While these attacks have the intention of stealing personally identifiable information from individual victims, the company’s being used and impersonated by threat actors also face consequences. Ironically, while brand impersonation of companies is used by threat actors to inspire and gain trust in victims, the companies being impersonated run the risk losing the trust of their customers, suppliers and any potential new hires. Therefore it is imperative that companies take part in and invest in the effort to ensure that threat actors limit exploitation of their brand to protect their reputation as a trusted brand.
At Bfore.Ai we have solutions to combat brand attacks similar to this and prevent long-term damage to your brand. Using predictive technology to evaluate and identify malicious domains before an attack is launched by the threat actor, we can rapidly identify threats and swiftly deploy countermeasures, stopping cybercriminals before their attack gets moving. Schedule a demo today to learn more about how Bfore.ai can help your company stop brand attacks to defend your reputation.