Brand Impersonated Search Engine Advertisements
%202.jpeg?width=800&height=536&name=Sans%20titre%20(11)%202.jpeg)
For years threat actors have used social engineering (SE) techniques to trick victims into revealing personal sensitive information for identity and monetary theft. One of the most well known tactics used within SE is phishing, wherein victims are contacted through online messaging platforms from seemingly reputable organisations encouraging the victim to either download a file or click on a link. To avoid this cybersecurity companies generally advise individuals to use a search engine (such as Google or Bing) to find the website they are looking for rather than clicking on a link in a suspicious email.
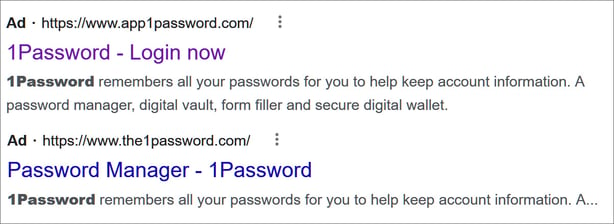
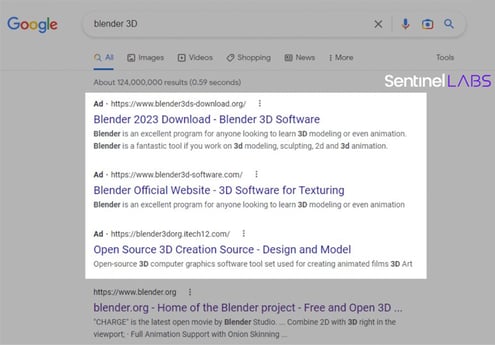
With individuals becoming more knowledgeable of phishing emails and how to identify them, threat actors have needed to find an alternate way of luring victims to their malicious websites. Since users, whether attempting to avoid a phishing email or not, generally use search engines to find almost everything they need, threat actors have increasingly started exploiting this sphere. They do so by impersonating brands in advertisements that appear in search engine results, such as in the screenshot below showing a brand impersonated search engine advertisement of the password manager, Bitwarden.
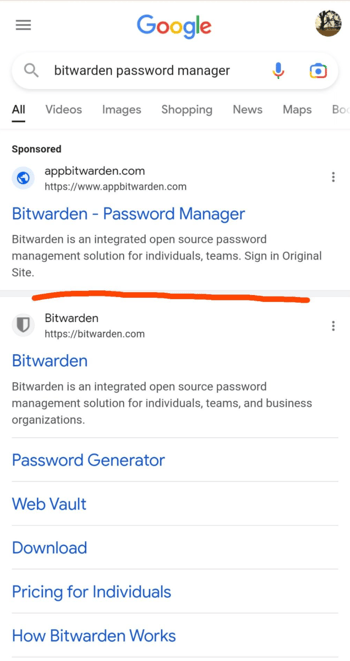 Source: Reddit
Source: Reddit
The two search results look very similar, however the URLs are quite different: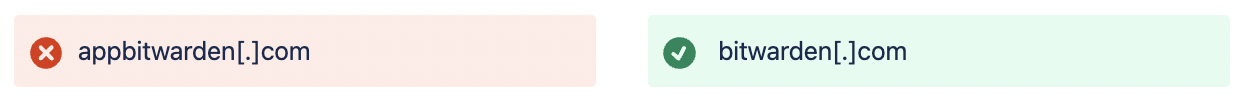
How do these brand impersonation scams work?
Brand impersonation is a tactic often deployed by threat actors wherein they use a brand's logo, colours, font, and so on, to ensure recognition and inspire trust with victims. As brands today all have some form of online presence (websites, mobile applications, social media accounts), replicating and impersonating a brand is a relatively simple task for threat actors to accomplish.
In these attacks, threat actors will have registered a domain similar to the targeted corporation before creating a fake website that through brand impersonation looks genuine and similar to the legitimate site if not a complete clone. They then use a search engine to buy advertisement spacing by creating a search campaign. Google’s pay-per-click (PPC) Ads platform, for example, has been frequently used in these attacks. So, when a user searches for a company or a service via a search engine, these advertisements will be displayed at the top of search results, often showcasing very little distinction between the brand impersonated advertisement and the genuine search result. An easy way to fool users.
Once a user clicks on the fake advertisement, they are directed to the brand impersonated website. These websites will pose different threats depending on the end goal of the attacker.
Fake Bank Login Sites
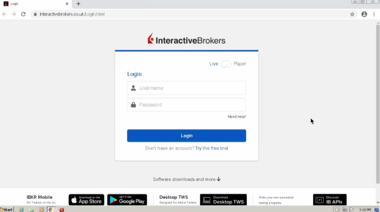
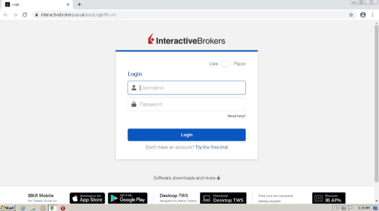
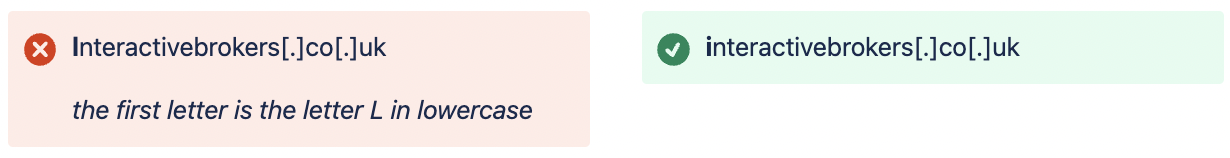
Some of these websites will showcase bank login pages such as the example below identified by Bfore.Ai where threat actors cloned the login page of American brokerage firm, Interactive Brokers. Here users are simply asked to login to their account allowing threat actors to steal these login credentials to conduct identity fraud and financial theft.
Malicious site Legitimate site
Fake Password Manager Login Sites
Password managers help keep track of a users passwords, keeping them safe in a ‘password vault’ that the user can access with a master password. If a threat actor gains access to your master password they will have access to all the passwords you have stored and effectively all your online accounts.
To steal these passwords, threat actors have most recently targeted password managers 1Password and Bitwarden through brand impersonated ads that lead users to cloned login sites.
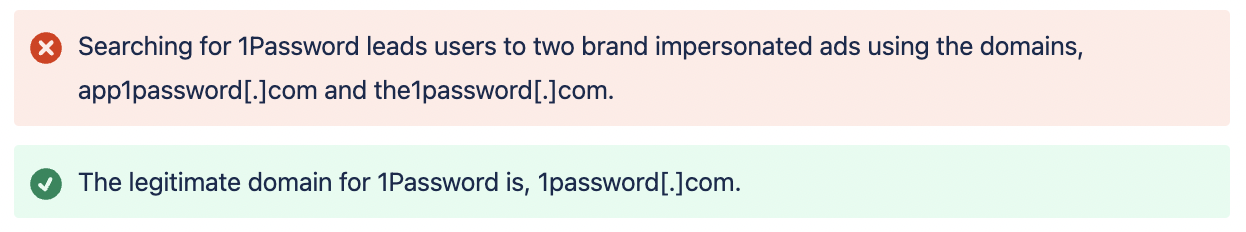
Source: MalwareHunterTeam
When searching for Bitwarden password manager on Google, users found a sponsored ad for Bitwarden with the domain appbitwarden[.]com, which when clicked on redirected users to the brand impersonated login site bitwardenlogin[.]com. As seen in the image below, the search results shows the sponsored brand impersonated ad above the legitimate company domain, making it likely that users will click on it.
![]()
 Source: Reddit
Source: Reddit
.png?width=379&height=230&name=c63c9240-895a-4e65-b820-b6d6c613b97d%20(1).png)
Trojanized Software
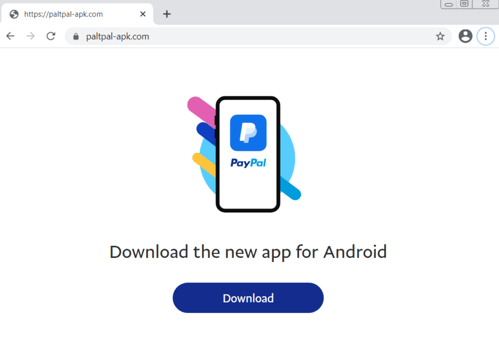
Another popular method utilised by threat actors has been using search engine advertisements to showcase brand impersonated websites of popular software products.
“Among the products impersonated in these campaigns include Grammarly, MSI Afterburner, Slack, Dashlane, Malwarebytes, Audacity, μTorrent, OBS, Ring, AnyDesk, Libre Office, Teamviewer, Thunderbird, and Brave.” BleepingComputer
Similar to the attacks above, threat actors trick users by registering a similar domain name and a clone of the legitimate software website. However, in these attacks, threat actors have inserted a trojanized version of the software that downloads onto a users computer when they click on a download button. The malware downloaded onto the users system includes many variants; Raccoon Stealer, IcedID, RedLine, and FormBook, which work as info stealers and banking trojans with a variety of features such as keylogging, screenshot theft, harvesting of credentials, and staging of additional malware.
Source: Sentinel Labs
 Source: BleepingComputer
Source: BleepingComputer
Recommendations for regular people:
-
Always double check the URL in an advertisement to make sure it is the legitimate one. As aforementioned, the URL will most likely be very similar to the intended URL but with with typos or a misplaced letter.
-
Instead of using a search engine to find a specific website, type the website into your internet browsers address bar. This usually guides you directly to the official website.
-
When conducting internet searches using a search engine, use ad blocking extensions.
Impact to your brand
While these attacks have the intention of stealing personally identifiable information from individual victims, the company’s being used and impersonated by threat actors in search results also face consequences. Ironically, while brand impersonation of companies is used by threat actors to inspire and gain trust in victims, the companies being impersonated run the risk losing the trust of their customers. Not knowing which link to trust on a search engine, may result in the user finding another solution. Therefore it is imperative that companies take part in and invest in the effort to ensure that threat actors limit exploitation of their brand to protect their reputation as a trusted brand.
Recommendations for corporations:
With more than 180,000 domains registered globally every day, identifying these malicious domains that are used to steal sensitive data, is the first step in preventing further attacks. However, this requires analysing every single domain registration to identify a malicious registration, which cannot be accomplished manually and requires specialised tools to efficiently and effectively analyse.
As recommended by the FBI, companies must use domain protection services where they can receive notifications when similar domains are registered in order to prevent these attacks. At Bfore.Ai we have the solution needed to combat these search engine brand attacks to prevent long-term damage to your brand. Using predictive technology to evaluate and identify malicious domains before an attack is launched by the threat actor, we can rapidly identify threats and swiftly deploy countermeasures, stopping cybercriminals before their attack gets moving. Schedule a demo today to learn more about how Bfore.Ai can help your company stop brand attacks to defend your reputation.
Additionally, ensure that your company educates employees about
-
where to safely download legitimate programs/software for business purposes, and
-
how to detect brand impersonated/scam websites and domains through Security Awareness trainings. Ensure that these trainings are up to date and include the newest social engineering tactics employed by threat actors.
Sources
-
The FBI says you need to use an ad blocker, hard to disagree
-
Bitwarden password vaults targeted in Google ads phishing attack
-
r/Bitwarden - Google Search Ads showing fake bitwarden web vault site as top result.
-
Hackers abuse Google Ads to spread malware in legit software
-
FormBook Malware Spreads via Malvertising Using MalVirt Loader to Evade Detection
-
Google ads push ‘virtualized’ malware made for antivirus evasion
-
MalVirt | .NET Virtualization Thrives in Malvertising Attacks
-
Typosquat campaign mimics 27 brands to push Windows, Android malware
.png?width=1200&height=627&name=Online%20Impersonation%20Ebook%20Blog%20Ad%20(1).png)


