[SCAM ALERT 063] - Stifel Financial Corp.
.png?width=797&height=332&name=SCAM%20ALERT%20(11).png)
Stifel is a diversified global wealth management and investment banking company focused on building relationships that help individuals, families, and organizations pursue their financial goals.
During our PreCrime internet scout of November 10th 2022 we identified suspicious markers across multiple vectors. One of those was this website spoof that could be targeting unsuspecting customers of Stifel Financial Corp.
The Attack
Target:
- Customers of Stifel Financial Corp.
Possible threats:
- Credential harvesting and financial gain - After luring users to the site, they are asked to login to their Stifel bank account using their credentials, allowing threat actors to take control of their bank account and steal their money. Customers may be led to the website via a phishing campaign, asking them to click on a link to resolve an issue with their account for example.
- Stifel Financial Corp. provides services for both individuals as well as institutions and corporations, companies connected to Stifel would also run the risk of stolen credentials. With 51% of people using the same passwords for both their work and personal accounts, any stolen credentials may provide threat actors with internal access to a company network leaving them vulnerable to financial loss, sensitive and confidential data leaking, as well as further cyber attacks such as ransomware.
With a yearly revenue of 4 billion USD, a data breach of Stifel Financial Corp. could result in the loss of up to 16 million USD!
|
Malicious sites: stbankweb[.]com |
Legitimate site: stifel[.]com
|
|
|
|
Technical Breakdown
Threat Indicators
-
Malicious domains impersonating Stifel Financial Corp. that attempts to trick visitors into sharing personal information
-
DNS records of malicious domain different to Stifel Financial Corp.
-
Newly registered site: November 8 2022
-
Domain validated SSL certificate
-
MX record indicates domain may be part of a phishing campaign
-
IP address with malicious activity
Detection and Threat Analysis
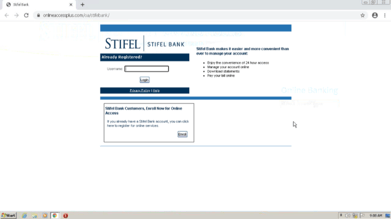
The malicious domain (stbankweb[.]com) is targeting Stifel Financial Corporation, an American multinational independent investment bank and financial services company that offers securities-related financial services in the United States and Europe through several wholly owned subsidiaries. The malicious domain was created November 8 2022 and identified by Bfore.Ai November 9, 2022.
-
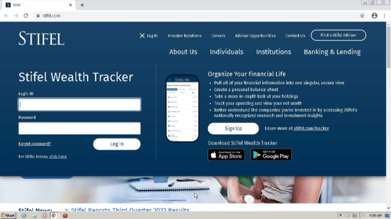
The malicious domain shows users a duplicate site of Stifel Bank. Here users have the option to login to their bank account using three different account types. Once clicking on the preferred account type, users are directed to another site where they can login using their credentials. Once completed, the threat actor will have stolen the users credentials and thereby have access to their bank account and personal information.
-
The DNS records are different to the DNS records of the legitimate website. The main point of interest is that the legitimate domain has registered their SSL Certificate and IP address under it’s own organisations name (Stifel Financial Corp/Stifel, Nicolaus & C), whereas the malicious domain does not specific an organisation name. Legitimate companies will always include their organisation name in DNS records in order to verify their legitimacy as Stifel Financial Corp. has done. See further details and comparison between the malicious and legitimate domain below.
-
The registered SSL certificate for the malicious domain is domain validated, meaning that the business on the site has not been validated as legitimate. The SSL certificate for the legitimate site which has been organization validated, meaning that the business has been validated as legitimate.
-
The domain has registered MX records, giving the threat actors the ability to accept and send email messages on behalf of the domain names. This indicates that the threat actors may be setting up the domain to be part of a phishing campaign that leads to the malicious domain.
-
The malicious domain resolves to an IP address that has been blacklisted by several servers, with several malicious .EXE (executable file for Windows operating system) and .RTF (files that allow advanced formatting to be viewed on multiple platforms) communicating files.
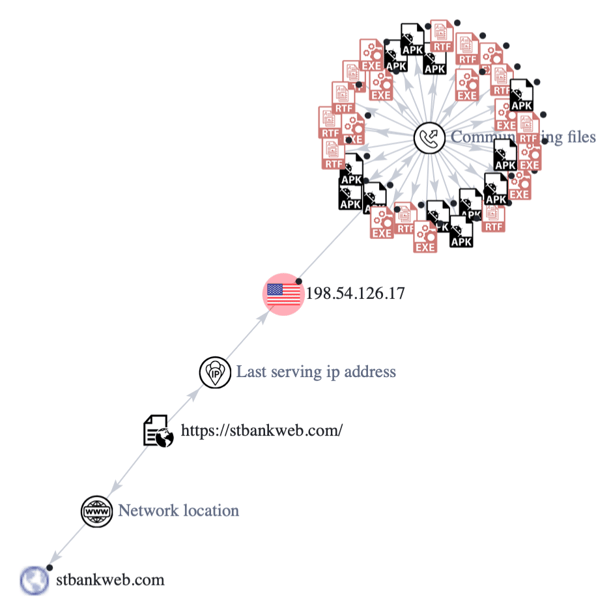 VirusTotal Graph
VirusTotal Graph
DNS Record
|
Domain |
stbankweb[.]com |
stifel[.]com |
|---|---|---|
|
Domain Creation and Expiration |
2 days old Created on 2022-11-08 |
10,038 days old Created on 1995-05-18 |
|
Registrar |
NameCheap, Inc. |
Network Solutions, LLC |
|
Registrar country |
Iceland |
United States |
|
Certificate |
Issued by: Sectigo Limited Issued to: The domain Domain validated 07-11-2022 -> 07-11-2023 Valid for 1 year |
Issued by: DigiCert Inc Issued to: Stifel Financial Corp Organization validated 28-03-2022 -> 04-04-2023 Valid for over 1 year |
|
Name Servers |
DNS1.NAMECHEAPHOSTING.COM DNS2.NAMECHEAPHOSTING.COM |
EDNS1.ULTRADNS.BIZ EDNS1.ULTRADNS.COM EDNS1.ULTRADNS.NET EDNS1.ULTRADNS.ORG |
|
MX record |
mx1-hosting.jellyfish.systems mx2-hosting.jellyfish.systems mx3-hosting.jellyfish.systems
Blacklisted:
|
smtp.gslb.stifel.com |
|
IP address |
198.54.126.17 New York, United States AS22612 Namecheap, Inc. ISP: Namecheap, Inc.
Blacklisted
|
8.26.184.110 Missouri, United States AS26471 Stifel, Nicolaus & C ISP: Stifel, Nicolaus & C |
|
Last seen active |
10 November 2022 |
10 November 2022 |
How Bfore.Ai is protecting our customers
At Bfore.Ai, we work daily to ensure these phishing attacks get stopped before even reaching their targets. We are here to make your internet journey safer than it has ever been.
With more than 30K new malicious indicators per day we got you covered no matter where the attack comes from. Only 0.05% false positive rate, stop wasting time in false alerts chasing. By launching our PreCrime and PreEmpt technologies, we measure our anticipation from an attack starting, faster than attackers.

Accepting that the only defense is good detection, is accepting to be forever a victim. We believe in prevention more than response. Visit our website for more information !
Bfore.Ai’s recommendations
Every day, adversarial tactics become more collaborative, technologically advanced, and rapid - and at this rate, you simply can’t afford to wait for the next attack before you react. Here are some recommendations from our team :
-
Pay close attention to the URL
-
Check connection security indicators (the lock)
-
Read emails carefully
-
Look for trust seals
Appendix
This document and its contents do not constitute, and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Bfore.Ai) is ultimately responsible for assessing and meeting Client's own compliance responsibilities. This report does not constitute a guarantee or assurance of Client's compliance with any law, regulation or standard.